
MistEye serves as the retina (threat perception), MistTrack as the immune system (on-chain risk control), OpenClaw security practices as the skeleton (behavioral constraints), MistAgent as the brain (deep analysis and auditing), and ADSS as the armor (full lifecycle protection), forming a comprehensive defense architecture.
As AI toolchains and Web3 businesses become deeply integrated, OpenClaw/Agents are evolving from supporting roles into core productivity nodes capable of directly executing high-privilege actions. At the same time, the attack surface has expanded from traditional code vulnerabilities to the prompt layer, tool supply chain, system execution layer, and on-chain asset layer, with risks exhibiting stronger linkage and destructiveness.
This solution takes the user’s OpenClaw/Agent as the security center and constructs a “five-layer progressive digital fortress” system: using ADSS (AI Development Security Solution) as the governance baseline, OpenClaw and similar tools as the execution carriers, and MistEye Skill, MistTrack Skill, and MistAgent as capability plugins injected into the execution chain. This enables a closed-loop security mechanism of “pre-check before execution, constraint during execution, and post-execution review.”
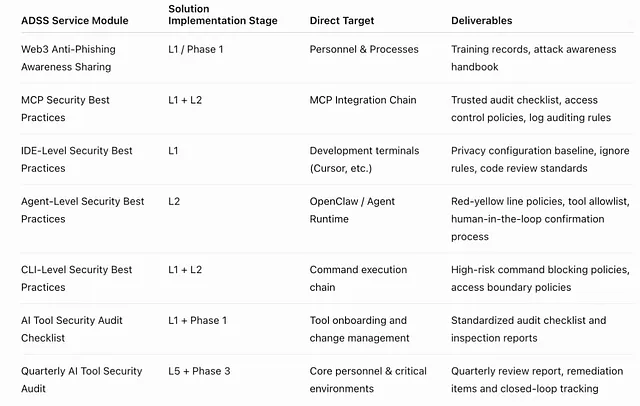
Among them, ADSS is not only a conceptual input layer but also the governance foundation and service framework of this solution, covering implementable modules such as: Web3 anti-phishing sharing, best security practices for Skills/MCPs, IDE-level security practices, Agent-level security practices, CLI-level security practices, AI tool security audit checklists, and quarterly AI tool security audits (four times per year).
The core value of this solution lies in systematically reducing risks such as data leakage, supply chain poisoning, erroneous execution, and on-chain asset loss — without sacrificing agent efficiency — while helping teams establish sustainable, auditable, and evolvable Agent security operation capabilities.
Key Takeaways
- The integration of AI toolchains and Web3 businesses introduces new attack vectors, expanding beyond traditional code vulnerabilities.
- A comprehensive security architecture, termed a “five-layer progressive digital fortress,” is proposed to protect AI Agents and Web3 operations.
- ADSS (AI Development Security Solution) serves as the foundational governance framework for this security system.
- MistEye, MistTrack, and MistAgent act as integrated security plugins (retina, immune system, brain) within the Agent’s execution chain.
- The system aims to create a closed-loop security mechanism: pre-checks, execution constraints, and post-execution reviews.
- Key risks addressed include data leakage, supply chain attacks, erroneous execution, and on-chain asset loss.
- Continuous operations through inspections, disaster recovery, and expert reviews are crucial for long-term security.
1.1 ADSS Concept and Problem Definition
ADSS (AI Development Security Solution) is a comprehensive security solution for AI toolchains and intelligent agent development scenarios. Its positioning is not a single-point product but a governance framework covering “personnel awareness, tool baselines, behavioral constraints, and audit review,” designed to control the new attack surfaces introduced as AI is rapidly adopted in business operations.
Core problems ADSS aims to solve
- Lack of a unified security baseline after introducing AI tools: Teams often use IDEs, CLIs, Agents, and Skills/MCPs simultaneously, but lack unified access standards and minimum-privilege boundaries.
- Lack of targeted protection against new attack surfaces: Including prompt injection, malicious MCPs, malicious Skills, open-source dependency poisoning, and context privilege escalation.
- Conflict between development efficiency improvements and security compliance: Without procedural auditing and inspection mechanisms, efficiency gains may come at the cost of privacy leakage, configuration drift, and incorrect automated execution.
- Lack of continuous review and expert auditing mechanisms: Many policies are configured only once during deployment and lack quarterly reviews and continuous optimization, leading to gradual policy failure.
Role of ADSS in this solution
- Serves as the governance foundation of the L1 infrastructure and policy layer
- Provides unified rule sources, audit standards, and operational cadence for L2–L5
- Ensures capabilities remain continuously effective through “Checklist + Quarterly Audit” rather than being a one-time implementation
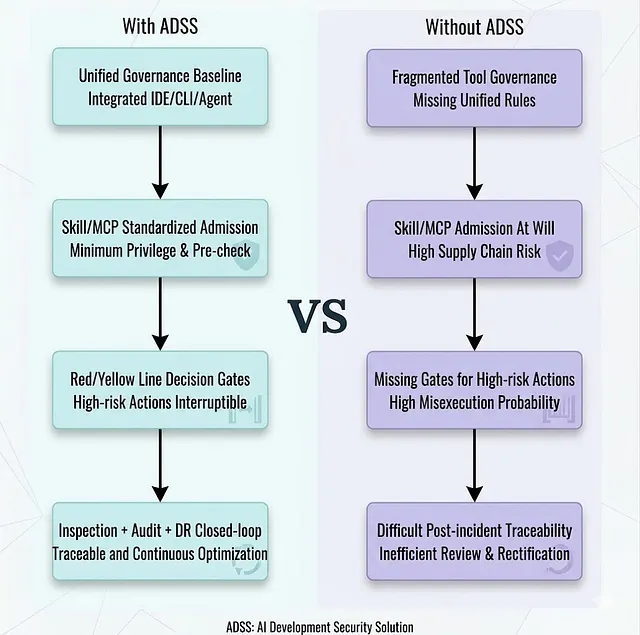
This comparison illustrates that the core value of ADSS lies in upgrading “scattered security actions” into a systematic security operations mechanism that is executable, auditable, and sustainable.
2. Background and Threat Landscape (AI × Web3 Cross Risks)
The current AI-driven development and autonomous execution environments face the following compound risks:
- Prompt injection and governance vacuum: Malicious context, code comments, or external documents can induce Agents to execute unintended actions, while traditional security monitoring struggles to cover instruction-layer risks.
- Supply chain poisoning 2.0 (Skills/MCPs/dependencies): Malicious Skills/MCPs, open-source repositories, and package dependencies have become new attack entry points, potentially embedding backdoors during installation or update stages.
- IDE/CLI environment privacy leakage: Without enforced privacy and ignore policies, sensitive information (.env, private keys, tokens, mnemonic phrases) may be indexed, exfiltrated, or abused.
- High-value Web3 action risks: When agents perform irreversible operations such as transfers, swaps, and contract calls, the lack of AML risk control and signature isolation may result in direct asset loss.
- High-privilege execution amplification: Agents can interact with local commands, browsers, and APIs. A single point of loss of control can rapidly escalate into system-level and asset-level incidents.
Therefore, the security objective is no longer simply “preventing vulnerabilities,” but ensuring that “Agents can execute in a controllable manner within high-privilege environments.”
3. Five-Layer Progressive “Digital Fortress” Overall Architecture

Layered objectives
L1: Establish security baselines for organizations, tools, and processes
L2: Constrain Agent permission boundaries and restrict high-risk behaviors
L3: Provide real-time threat perception and pre-checks for external interaction entry points
L4: Strengthen on-chain risk determination and deep analysis of complex events
L5: Form a long-term stable operational closed loop through inspections, disaster recovery, and expert reviews
4. Five-Layer Capability Description (L1–L5)
L1: Infrastructure and Policy Layer (ADSS Baseline Governance)
L1 uses ADSS as the sole governance parent body. All control items are decomposed and validated through ADSS service modules:
- Web3 anti-phishing sharing: Combines frontline phishing/APT techniques for awareness training to improve team recognition of AI-enhanced scams (such as deepfake meetings).
- Best security practices for Skills/MCPs: Establish trusted review of third-party Skills/MCPs, sandbox isolation, least privilege, and interaction log auditing mechanisms.
- IDE-level security practices (e.g., Cursor): privacy mode, .cursorignore rules, Rules constraints, prompt injection protection, and generated code review processes.
- Agent-level security practices (e.g., OpenClaw): Skill auditing, tool whitelists, human-in-the-loop confirmation for critical actions, and restricted wallet/signature interface permissions.
- CLI-level security practices (e.g., Claude Code): secondary confirmation for high-risk commands, root directory access restrictions, and Shell history auditing.
- AI tool security audit checklist: tool access and review conducted across four dimensions — supply chain, data privacy, permission control, and output compliance.
- Quarterly AI tool security audits: once per quarter (four times per year), expert reviews and configuration verification for core members’ AI tool environments.
L2: Agent Governance Layer (e.g., Zero-Trust Constraints for OpenClaw)
- Red-line/yellow-line behavior protocols and human–machine confirmation mechanisms
- Core configuration permission narrowing and hash baselines (to prevent configuration drift and abnormal tampering)
- Pre-audit before introducing Skills/MCPs, following the principles of least privilege and traceability
L3: Real-Time Intelligence Perception Layer (MistEye Skill)
MistEye Skill functions as the Agent’s “real-time threat retina,” providing rapid threat pre-checks before execution:
- URL/domain/IP security detection
- Pre-check of open-source repositories and dependency sources
- Security scanning before installing Skills/MCPs
- Trigger blocking or escalation to human confirmation when high-risk intelligence is detected
L4: Expert Analysis and Risk Control Layer (MistTrack Skill + MistAgent)
This layer handles “high-value actions” and “complex suspicious events”:
- MistTrack Skill: provides on-chain AML risk analysis capabilities, supporting address risk scoring, fund relationship analysis, and transaction pre-risk checks.
- MistAgent: acts as a deep security analysis hub, performing multi-dimensional threat analysis and contextual assessment on Agent access targets, files, and contracts.
Key principle: signature isolation. Agents only construct unsigned transaction data and do not touch plaintext private keys; actual signing is performed by humans in independent wallets.
L5: Continuous Operations and Response Layer (Inspection + Disaster Recovery + Expert Review)
- Nightly automated inspections with explicit reporting (reports must be generated even if no anomalies are detected).
- Disaster recovery synchronization of security states and key configurations to ensure recoverability.
- Quarterly expert-level audits and attack–defense validation to continuously correct strategic blind spots.
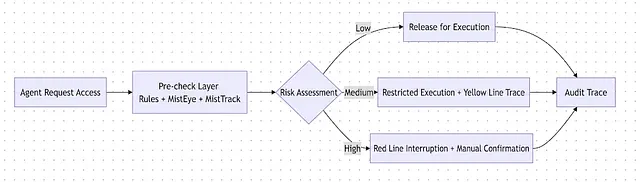
5. Closed-Loop Core Scenarios (Installing Skills/MCPs / Accessing URLs / On-Chain Transactions)
Three high-frequency scenarios share the same security closed loop:
Agent initiates action → pre-check → risk assessment → allow / restrict / interrupt → audit logging
Scenario A: Installing Skills or Connecting MCPs
- Agent initiates installation request.
- MistEye Skill performs pre-checks (source, content, suspicious behavior patterns).
- If high-risk intelligence is detected, the process is interrupted and an alert is issued; low-risk cases proceed to controlled installation.
- Installation results and related actions are written into audit logs.
Scenario B: Accessing URLs or Pulling Open-Source Repositories
- Agent initiates access or download request.
- MistEye Skill performs security detection on the URL/domain/repository.
- If the result is complex or conflicting, it is escalated to MistAgent for deep analysis.
- Based on the analysis conclusion, execution is allowed, restricted, or blocked.
Scenario C: On-Chain Transactions and Contract Calls
- Agent constructs transaction parameters.
- MistTrack Skill performs address and transaction risk verification.
- High-risk cases trigger a hard interruption and human confirmation.
- After approval, humans sign in an independent wallet; the Agent never accesses private keys.
6. Key Technical Implementation Blueprint
6.1 Control Flow: From Request to Handling
6.2 Data Flow: Aggregation of IOC, On-Chain Risk, and Behavioral Logs
- Input layer: IOC intelligence, on-chain address risk data, command and network behavior logs, extension installation change records.
- Processing layer: real-time pre-checks, rule matching, event correlation, deep analysis.
- Output layer: execution decisions, response recommendations, audit evidence, inspection reports.
6.3 Decision Flow: Red Line, Yellow Line, and Human–Machine Confirmation
- Red line: destructive commands, sensitive information exfiltration, extremely high-risk on-chain targets → mandatory interruption.
- Yellow line: privilege escalation, environment changes, critical system operations → execution allowed but mandatory logging.
- Escalation condition: when pre-check results are uncertain or contexts are complex, MistAgent is invoked for further analysis and verification.
6.4 System Boundaries: Local Execution Domain and External Capability Domain
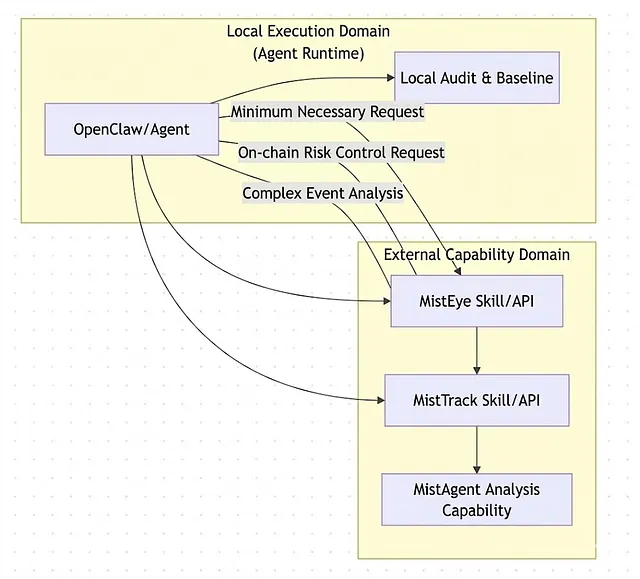
Boundary principle: only the minimum necessary fields are transmitted; sensitive context remains local by default, while external capabilities are invoked on demand with full logging.
7. Phased Implementation Roadmap (Phase 0–3)
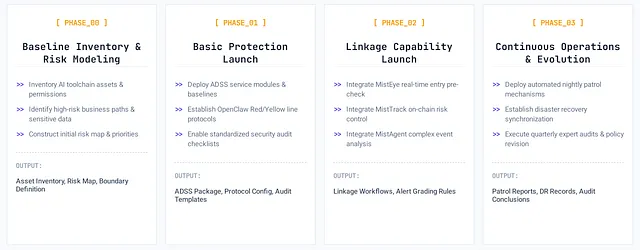
Phase 0: Baseline Inventory and Risk Modeling
- Inventory assets, permissions, existing AI toolchains, and critical business paths.
- Identify high-risk actions, sensitive data, and key dependencies.
- Form an initial risk map and priority list.
Output: asset inventory, risk map, boundary definition documentation
Acceptance: high-risk links and sensitive assets fully identified
Phase 1: Basic Protection Deployment
- Implement ADSS service modules (anti-phishing, MCP, IDE, Agent, CLI, Checklist)
- Establish red/yellow line protocols and least-privilege configurations for Agents (e.g., OpenClaw)
- Enable standardized AI tool audit checklists and access processes
Output: ADSS deployment package (training records, policy documents, configuration baselines, audit templates)
Acceptance: high-risk actions have interruption mechanisms; yellow-line actions have logging capabilities
Phase 2: Integrated Capability Deployment
- Integrate MistEye Skill into pre-checks for installation, access, and download entry points
- Integrate MistTrack Skill into pre-transaction on-chain risk control
- Integrate MistAgent into complex event analysis and response recommendation chains
Output: integrated workflows, alert classification rules, response playbooks
Acceptance: closed-loop decision-making and auditing implemented for three core scenarios
Phase 3: Continuous Operations
- Deploy nightly automated inspections and explicit briefing mechanisms
- Establish security state disaster recovery synchronization mechanisms
- Execute quarterly ADSS expert audits and policy revisions (four times per year)
Output: inspection reports, disaster recovery records, quarterly audit conclusions
Acceptance: a stable operational loop of “detection → analysis → response → review” is established
8. Advanced Capabilities and Evolution Direction (High-Level Roadmap)
Rule-driven → intelligence-driven
Continuously introduce real-time threat intelligence feedback to dynamically update decision strategies.
Point security → end-to-end security orchestration
Bring IDEs, CLIs, Agents, and on-chain execution into the same policy domain for unified governance.
Manual response → semi-automated response
Automatically interrupt high-confidence risks while retaining final human confirmation for critical decisions.
Capability expansion directions
Introduce real-time host detection (HIDS/inotify), a unified risk scoring engine, and Policy-as-Code to achieve strategy versioning and rollback capability.
Appendix: Explanation of the Solution’s Main Framework
This solution does not treat MistEye Skill, MistTrack Skill, and MistAgent as parallel and isolated capabilities. Instead, they are unified within the execution chain of the target user’s Agent (such as OpenClaw):
- MistEye Skill is responsible for “detecting threats/risks first.”
- MistTrack Skill is responsible for “first determining on-chain threats/risks.”
- MistAgent is responsible for “deeply understanding complex threats/risks.”
The ultimate goal is to enable Agents to possess secure execution capabilities that are perceptible, controllable, auditable, and recoverable in high-value scenarios.
Appendix: Mapping of ADSS Services to the Implementation of This Solution
Open-Source Community Tool:
AI-Infra-Guard
A one-stop AI red team security testing platform that enables routine security self-checks during daily use, helping identify potential vulnerabilities in AI deployments.
SlowMist AI Security Open-Source Resources
To help developers and teams build safer development and operational environments for AI Agents and Web3 scenarios, SlowMist has continuously open-sourced a number of AI security tools and practical resources for community reference and use:
OpenClaw Security Practice Guide
An end-to-end Agent security deployment manual covering everything from the cognition layer to the infrastructure layer. It systematically outlines security practices and deployment recommendations for high-privilege AI Agents in real-world production environments.
MCP Security Checklist
A systematic security checklist designed to quickly audit and harden Agent services, helping teams avoid missing critical defense points when deploying MCPs/Skills and related AI toolchains.
MasterMCP
An open-source malicious MCP server example used to reproduce real attack scenarios and test the robustness of defense systems. It can be used for security research and defense validation.
MistTrack Skills
A plug-and-play Agent skill package that provides AI Agents with professional cryptocurrency AML compliance and address risk analysis capabilities, enabling on-chain address risk assessment and pre-transaction risk evaluation.
These open-source resources help developers better understand AI Agent security risks, attack paths, and defensive practices in real-world environments, and serve as important references for building secure AI toolchains.
If your team is exploring AI Agent security deployment, Web3 security governance, or enterprise-level AI security architecture development, SlowMist can provide relevant security consulting and technical support services. If you are interested in the comprehensive security solution proposed in this article or would like to learn more about its practical implementation, please feel free to contact the SlowMist security team. (Email: [email protected])
About SlowMist
SlowMist is a threat intelligence firm focused on blockchain security, established in January 2018. The firm was started by a team with over ten years of network security experience to become a global force. Our goal is to make the blockchain ecosystem as secure as possible for everyone. We are now a renowned international blockchain security firm that has worked on various well-known projects such as HashKey Exchange, OSL, MEEX, BGE, BTCBOX, Bitget, BHEX.SG, OKX, Binance, HTX, Amber Group, Crypto.com, etc.
SlowMist offers a variety of services that include but are not limited to security audits, threat information, defense deployment, security consultants, and other security-related services. We also offer AML (Anti-money laundering) software, MistEye (Security Monitoring), SlowMist Hacked (Crypto hack archives), FireWall.x (Smart contract firewall) and other SaaS products. We have partnerships with domestic and international firms such as Akamai, BitDefender, RC², TianJi Partners, IPIP, etc. Our extensive work in cryptocurrency crime investigations has been cited by international organizations and government bodies, including the United Nations Security Council and the United Nations Office on Drugs and Crime.
By delivering a comprehensive security solution customized to individual projects, we can identify risks and prevent them from occurring. Our team was able to find and publish several high-risk blockchain security flaws. By doing so, we could spread awareness and raise the security standards in the blockchain ecosystem.
Based on materials from : slowmist.medium.com
