Supply Chain Attack Exploits Apifox CDN to Steal Credentials
The security team at SlowMist has identified a sophisticated supply chain attack that compromised a front-end script file hosted on Apifox’s official Content Delivery Network (CDN). Malicious JavaScript code, heavily obfuscated, was injected into the legitimate script located at hxxps://cdn.apifox.com/www/assets/js/apifox-app-event-tracking.min.js. This malicious code disguised itself as standard analytics tracking functionality. When executed within the Apifox Electron desktop client, it was designed to steal user authentication credentials and sensitive system information, transmitting them to an attacker-controlled Command and Control (C2) server. The ultimate goal was to achieve Remote Code Execution (RCE) by retrieving and running arbitrary commands.
Key Takeaways
- A supply chain attack targeted Apifox’s official CDN, injecting malicious JavaScript into a legitimate script file.
- The malware steals user authentication credentials and sensitive system information from the Apifox Electron desktop client.
- The attackers achieved Remote Code Execution (RCE) capabilities.
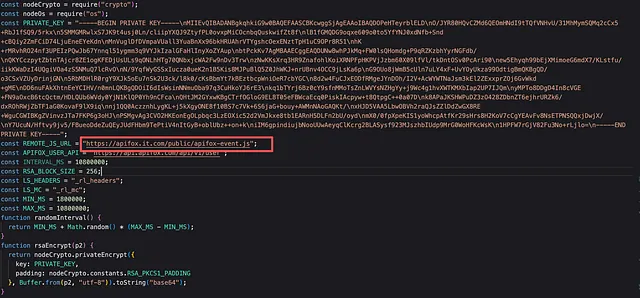
- The malicious code employed heavy obfuscation, RC4 encryption for strings, multi-step computations for constants, and RSA encryption for C2 communications.
- Affected users are advised to revoke access tokens, log out and re-login, change passwords, block malicious domains, and clear specific local storage data.
Analysis of the Injection Vector
The initial point of compromise was the manipulation of resources on Apifox’s official CDN. The attack substituted the legitimate resource with a malicious version that contained obfuscated code alongside the original analytics logic. This enabled the theft of data and facilitated remote control over the infected client.
A comparison between the legitimate and the compromised script, as analyzed from web archives, reveals the embedded malicious segment designed for information theft and remote control.
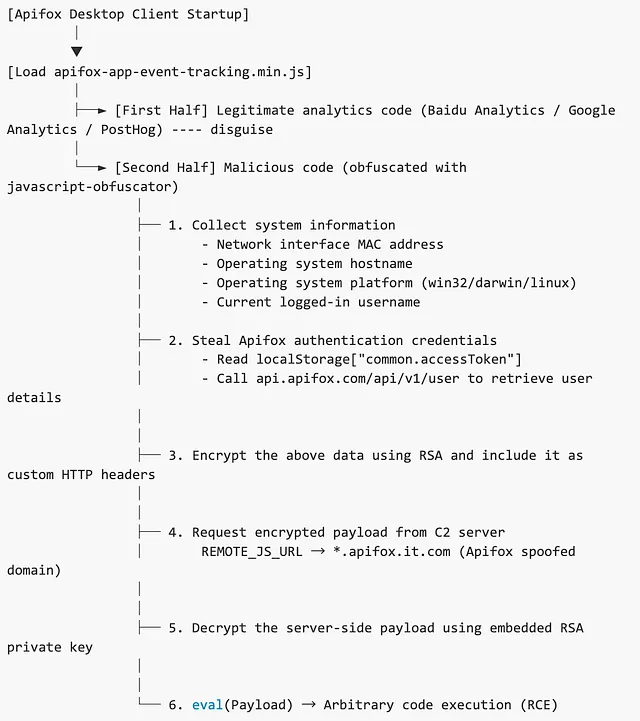
The attack flow diagram illustrates how the compromised script, loaded by the Apifox Electron client, initiated the malicious activities.
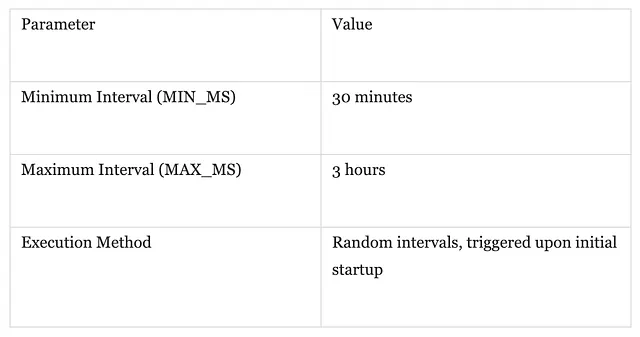
The malicious code incorporated a randomized timer to execute periodically, ensuring continuous data exfiltration and retrieval of updated payloads from the C2 server.
Obfuscation and Anti-Detection Techniques
- The malicious JavaScript code was heavily obfuscated using javascript-obfuscator.
- All strings within the code were encrypted using the RC4 algorithm and stored in an array, decrypted dynamically during runtime.
- Critical numeric constants were deliberately complexified through multi-step computations to hinder static analysis.
- Command and Control (C2) communications were encrypted using RSA, with an embedded private key to prevent traffic analysis.
- The malicious code was appended to the end of legitimate analytics code, attempting to bypass security measures by leveraging established trust.
Recommendations
For affected users:
1. Immediately revoke any historical access tokens used with Apifox and review API call records for suspicious activity.
2. Log out of your Apifox account and log back in to ensure current tokens are invalidated.
3. Change your Apifox account password and monitor for any unusual login attempts.
4. At the network level, block the domain ‘apifox.it.com’ and all its subdomains.
5. Clear the Apifox client’s localStorage and delete the ‘_rl_headers’ and ‘_rl_mc’ keys by executing the following commands in the Apifox client’s developer tools console:
localStorage.removeItem(‘_rl_headers’); localStorage.removeItem(‘_rl_mc’);
IoCs
Domain
apifox.it.com
*.apifox.it.com
URL
hxxp://cdn.apifox.com/www/assets/js/apifox-app-event-tracking.min.js
hxxp://cdn.apifox.com/www/assets/js/user-tracking.min.js
File
filename: apifox-app-event-tracking.min.js
SHA256: 91d48ee33a92acef02d8c8153d1de7e7fe8ffa0f3b6e5cebfcb80b3eeebc94f1
About SlowMist
SlowMist is a prominent blockchain security threat intelligence company established in January 2018. Founded by seasoned cybersecurity professionals with over a decade of experience, SlowMist aims to enhance global blockchain security. The firm has a strong reputation, having provided security services for numerous well-known projects and exchanges, including HashKey Exchange, OSL, MEEX, BGE, BTCBOX, Bitget, BHEX.SG, OKX, Binance, HTX, Amber Group, and Crypto.com.
SlowMist offers a comprehensive suite of security services, encompassing security audits, threat intelligence, defense deployment, and consulting. Their product offerings include Anti-Money Laundering (AML) software, MistEye for security monitoring, SlowMist Hacked (a database of cryptocurrency hacks), and FireWall.x, a smart contract firewall. They also maintain strategic partnerships with industry leaders like Akamai, BitDefender, and RC². Their expertise in investigating cryptocurrency-related crimes has been recognized by international bodies, including the United Nations Security Council and the UN Office on Drugs and Crime.
By delivering tailored and robust security solutions, SlowMist assists projects in identifying and mitigating potential risks. The firm has a track record of discovering and disclosing critical blockchain security vulnerabilities, contributing to higher security standards across the entire blockchain ecosystem.
Original article : slowmist.medium.com
