
- Goertzel states his team possesses the capability to regenerate Google’s undisclosed quantum attack circuits.
- The ASI Alliance CEO emphasizes that maintaining quantum capabilities in secrecy provides only a minimal advantage.
- According to Goertzel, Google’s 41% Bitcoin attack model already indicates a fundamental flaw in current cryptographic math.
Dr. Ben Goertzel, CEO of the Artificial Superintelligence (ASI) Alliance, has asserted that his organization can reconstruct the quantum attack circuits developed by Google Quantum AI, which the latter has chosen not to publicly release. Goertzel cautions that if his team can achieve this, then nation-state actors with sufficient resources likely already possess the same capability.
A whitepaper published by Google on March 30th indicated that functional circuits capable of executing Shor’s algorithm to break 256-bit elliptic curve cryptography could be constructed using fewer than 500,000 physical qubits. The Google team opted to publish a zero-knowledge proof instead of the actual code. However, Goertzel informed BeInCrypto that this decision does not alter the fundamental accessibility of the technology.
“Keeping Capabilities Secret Buys You at Most a Very Short Window”
Google characterized its decision to withhold the circuits as a measure of responsible disclosure, deviating from its usual practice of full transparency due to concerns about potential misuse. This stance sparked considerable debate within the cryptocurrency community regarding its alignment with the principle of “don’t trust, verify.”
Goertzel, however, dismissed these concerns, stating that the secrecy is functionally insignificant. He elaborated:
We are confident that we could regenerate the ‘secret circuit’ Google found using our own expertise and reasonable compute, and if we can do it, the Chinese government and other well-resourced actors certainly can too. Keeping capabilities secret buys you at most a very short window.
He further noted that the ASI Alliance has not withheld any of its own code for safety reasons, despite internal discussions on the matter. Goertzel’s default approach is one of openness, arguing that the benefits of decentralized scrutiny outweigh the limited risk reduction offered by secrecy when parallel discovery is probable.
An exception, he clarified, would be made for any development posing a specific, acute, short-term danger. However, he does not believe Google’s circuit falls into that category, given the widespread availability of the underlying knowledge to capable entities.
The 41% Problem
The Google whitepaper outlines a hypothetical “on-spend attack.” In this scenario, a quantum computer could pre-compute parts of a calculation, enabling it to break a Bitcoin (BTC) transaction in approximately nine minutes after the public key is revealed. Given that the average Bitcoin block confirmation time is around 10 minutes, this presents an attacker with a roughly 41% chance of completing the operation before the transaction is finalized.
The paper estimates that approximately 6.9 million BTC are currently held in wallets where public keys have been exposed in some manner. This includes around 1.7 million BTC from Bitcoin’s early years, as well as funds affected by address reuse and Bitcoin’s Taproot upgrade, which exposes public keys by default.
Goertzel considers a 41% attack success rate to be a critical vulnerability rather than a marginal risk. He stated:
Any attack success rate above single digits is deeply problematic for a store-of-value chain. Once rational actors believe there is a meaningful probability that a transaction can be reversed or an address drained during the confirmation window, the game-theoretic assurances that underpin Bitcoin’s security model collapse. At 41%, you are well past the threshold.
While the necessary hardware for such an attack does not yet exist, Goertzel emphasized that the mathematical proof is complete. Google has set a 2029 deadline for the industry to transition to post-quantum cryptography (PQC). Currently, Bitcoin lacks a unified upgrade roadmap to meet this deadline.
ASI Alliance Says It Was Built for This
While much of the industry was engaged in debate, Goertzel indicated to BeInCrypto that his team had anticipated this scenario years in advance. He has previously forecast the potential arrival of human-level artificial general intelligence (AGI) around 2027 or 2028.
The convergence of Google’s quantum timeline and the predicted advent of AGI creates a critical juncture, and Goertzel stated that the ASI Alliance designed its infrastructure precisely for this eventuality. He explained:
The convergence of AGI and quantum computing is very real, but framing it as purely a ‘threat’ misses the other half of the picture. At the ASI Alliance we have been designing ASI:Chain from the ground up to be quantum-oriented–not just quantum-resistant but quantum-leveraging…So for us, quantum computing arriving alongside AGI is a feature, not a bug.
ASI:Chain, the layer-1 blockchain currently under development by the Alliance, utilizes MeTTa as its smart contract language instead of Solidity. According to Goertzel, MeTTa incorporates quantum-type systems, and the team has developed quantum versions of core Hyperon AGI algorithms covering attention allocation, probabilistic logic, and evolutionary learning.
The blockchain’s encryption layer is designed to be modular, allowing for the integration of quantum-safe cryptographic primitives, including lattice-based and hash-based schemes, without necessitating a chain redesign or a hard fork. Goertzel acknowledged that this approach introduces computational overhead, presenting a significant engineering challenge but not an architectural one.
The Artificial Superintelligence Alliance (FET) was established through a token merger involving SingularityNET, Fetch.ai, Ocean Protocol, and CUDOS. Ocean Protocol subsequently exited the merger, a development that led to legal proceedings amid allegations of token theft.
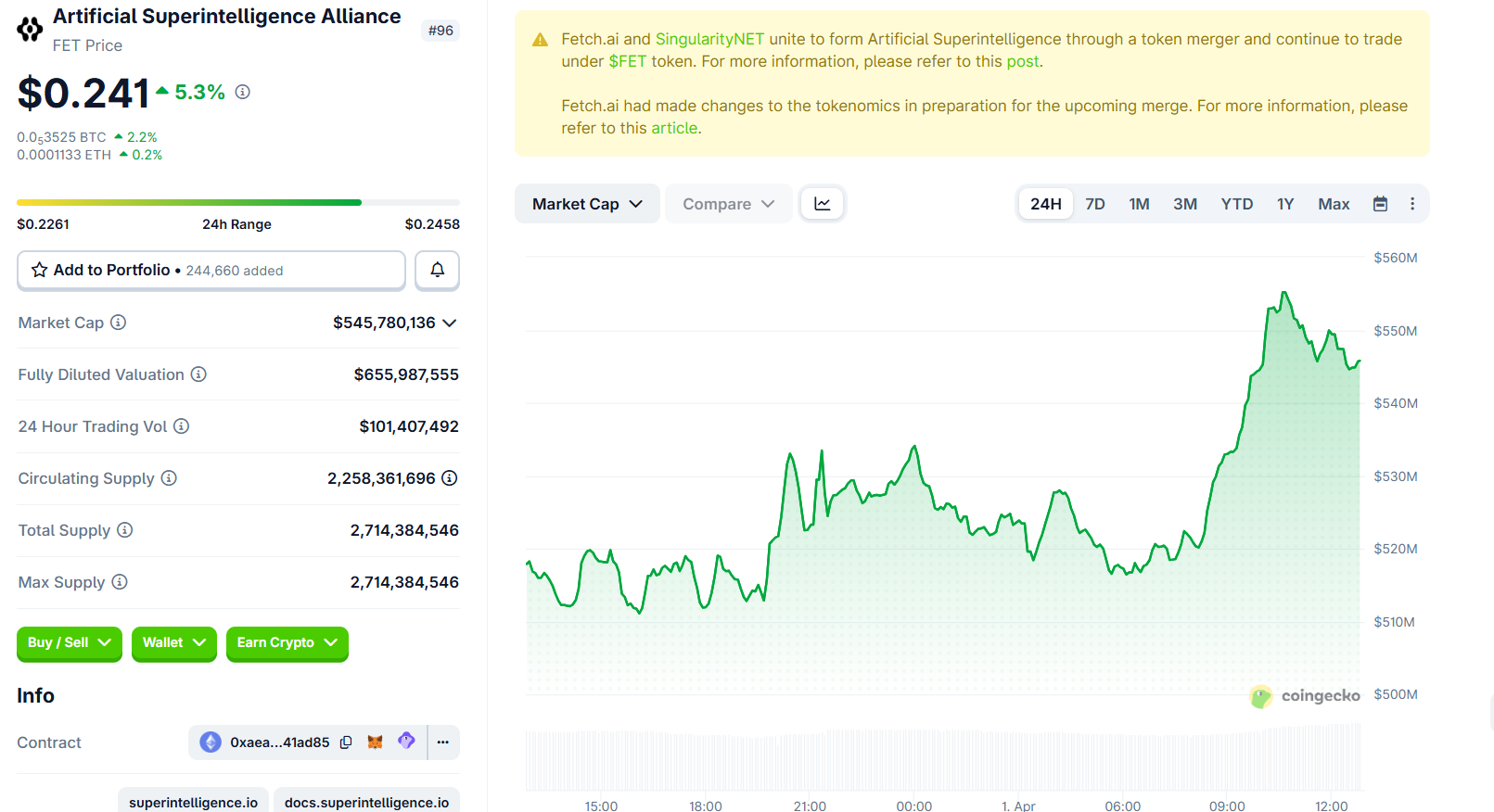
The FET token is currently trading at approximately $0.241, reflecting an increase of over 5% in the past 24 hours.
“A Catastrophic Precedent for Digital Property Rights”
Google’s whitepaper highlighted approximately 1.7 million BTC held in Satoshi-era Pay-to-Public-Key (P2PK) wallets, which permanently expose their public keys. These coins are considered irretrievable as their owners are either unknown or unreachable. The paper proposed a “digital salvage” framework that could grant governments the legal authority to quantum-crack these dormant coins.
Goertzel strongly opposes this proposition, stating:
On principle, no–giving governments a legal pathway to crack private wallets sets a catastrophic precedent for digital property rights. The entire value proposition of crypto rests on the idea that your keys are your coins. Once you establish that a sufficiently powerful actor can legally seize coins whose owners are absent, you have undermined the foundation.
He acknowledged that these coins will inevitably be accessed by someone. The critical question, in his view, is whether this process will be governed by a legal framework or descend into a free-for-all. Goertzel advocates for leaving dormant coins untouched as a matter of principle, allowing the ecosystem to account for their eventual vulnerability.
Binance co-founder Changpeng Zhao (CZ) presented an alternative perspective, suggesting that if Satoshi’s coins remain untouched for a specific duration, the community might consider locking or burning these addresses to prevent hackers from accessing them.
Saw some people panicking or asking about quantum computing’s impact on crypto. At a high level, all crypto has to do is to upgrade to Quantum-Resistant (Post-Quantum) Algorithms. So, no need to panic. 😂 In practice, there are some execution considerations. It’s hard to…
Zhao also noted the inherent difficulty in precisely identifying all of Satoshi’s addresses without conflating them with those of early legitimate holders.
The Race Is Already On
Venture capitalist Chamath Palihapitiya described Google’s paper as “quite reasonable” and urged the cryptocurrency community to establish a quantum-resistance roadmap within the next few years.
I mentioned this last year on @theallinpod and the crypto bros freaked out. Two things are true about crypto bros: they are extremely technical and extremely belief oriented. Sometimes, though, the latter clouds the former. This paper from Google, though, is quite reasonable…
CZ indicated that cryptocurrency would endure the quantum era but cautioned that coordinating upgrades across decentralized networks would likely lead to disputes, forks, and potentially new security vulnerabilities.
Goertzel’s outlook is more direct: he told BeInCrypto that projects capable of surviving will be those that began quantum-related engineering years ago. He believes that projects starting only after the first coins are compromised will not succeed.
In light of these developments, his practical advice for retail investors is to move their holdings to addresses utilizing the most recent key formats. For Bitcoin, this means using native SegWit (bech32) addresses, where the public key remains concealed until a transaction is initiated. He also advises against address reuse. For Ethereum (ETH), the vulnerabilities are more systemic, and individual mitigation options remain limited.
When questioned whether the quantum threat fundamentally undermines the decentralization thesis, Goertzel stated that it does not, but it significantly raises the stakes. He posited that if a centralized entity were to crack dormant Bitcoin and seize substantial assets, it would create a powerful centralizing force. However, he maintained that the decentralization thesis was never predicated on the indefinite longevity of legacy cryptography.
The decentralization thesis survives if decentralized projects out-engineer centralized ones on the quantum transition. That is exactly what we intend to do.
Google’s paper, alongside a separate study from Caltech and Oratomic demonstrating Shor’s algorithm’s execution at a cryptographic scale with 10,000 qubits, suggests that the window for preparation is narrower than widely assumed. Goertzel claims his team is already past this critical phase, positioning the rest of the industry in a race to adapt.
Information compiled from materials : beincrypto.com
