I’ve been covering crypto long enough to know that every bull cycle has its bloodbath moment. A rug here, a bridge exploit there. You learn, you move on. But April 2026 was different. This wasn’t one bad week. It was 30 straight days of protocols getting drained, wallets emptied, and communities left holding nothing but a post-mortem thread and an “investigation is ongoing.” Over $629 million gone — in a single month. I’ve never seen anything like it. And if you’re farming DeFi, bridging assets, or staking anywhere on-chain right now, you need to read this.
April 2026: The Most Devastating Month in DeFi History
Let’s start with the numbers, because they’re genuinely shocking.
April 2026 officially became the worst month for crypto hacks ever recorded. According to DeFiLlama data, over $629 million was drained from DeFi protocols across more than 25 separate incidents. To put that in context — that’s 3.7 times the total losses from the entire first quarter combined.
Two attacks alone made up almost all of it.
Drift Protocol on Solana lost $285 million on April 1st. Authorities linked it to North Korea’s Lazarus Group. But here’s the part that should scare you — it wasn’t a code exploit. The attackers spent six months building relationships with team members, embedding themselves into the project, and eventually gaining access to signing keys.
Then came KelpDAO on April 19th. $292 million gone. The attacker used Tornado Cash to fund a wallet, tricked LayerZero’s bridge contract into accepting a fake cross-chain message, and walked away with 116,500 rsETH — roughly 18% of the entire circulating supply.
Aave, one of DeFi’s most trusted lending platforms, got caught in the crossfire. Users panicked and rushed to withdraw, creating a liquidity crunch that rippled across the ecosystem.
And it didn’t stop there. Smaller exploits kept coming — every single day after April 25th saw at least one new incident. Volo Protocol on Sui lost $3.5 million. Scallop Lending lost $140,000. CoW Swap lost $1.2 million to a domain hijacking attack.
This wasn’t a fluke. This was a pattern.
The Attack Surface Has Completely Changed
For years, DeFi hacks followed a familiar script. Someone finds a bug in a smart contract. They drain the pool. Project scrambles to patch it.
That playbook is outdated.
The attacks that caused the most damage in April weren’t smart contract bugs at all. As one on-chain analyst put it — “Drift and Kelp weren’t code bugs. They were months of social engineering against humans with admin keys. No audit catches that.”
Think about what that means for you as a user. Even if a protocol has been audited five times, if one person on the team gets phished, your money could be gone.
The new attack vectors breaking through in 2026 are:
Cross-chain bridges. They hold massive reserves of locked assets and rely on complex cross-chain messaging that’s almost impossible to fully verify. When a bridge breaks, the attacker can drain the entire reserve backing wrapped tokens across multiple chains in a single transaction. Kelp’s LayerZero route was configured as a single point of failure. That’s all it took.
Oracle manipulation. Protocols that rely on third-party price feeds can be tricked into accepting bad data. Flash loans are frequently used to spike prices on low-liquidity tokens, distort oracle readings, and drain lending pools.
Social engineering against key holders. The most dangerous attack surface in 2026 isn’t code. It’s people. Multisig signers, core team members, developers with admin privileges — these are the real targets now. A six-month relationship-building campaign before a single exploit. That’s the new meta.
Domain hijacking. CoW Swap’s $1.2 million loss in April came from a hijacked domain. Users thought they were interacting with the real protocol. They weren’t.
Learn how compounding works, consistant small wins built quicker then you think.
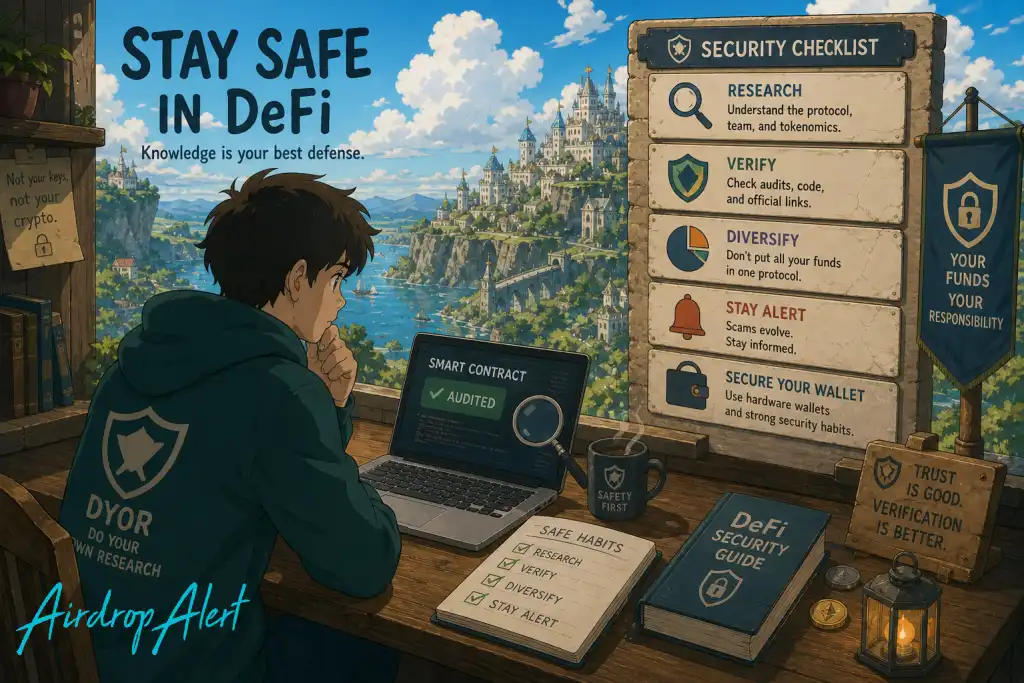
How to Protect Yourself: A Practical DeFi Security Checklist
Here’s the good news. You’re not helpless. Most retail users who lost money in April made one of a handful of very avoidable mistakes. Let’s go through each one.
1. Reduce Your Bridge Exposure — Seriously
Bridges have produced two of the three largest DeFi exploits in 2026 alone. The structural weakness hasn’t changed since 2022 — attackers just keep hitting them because the TVL keeps growing.
What to do:
- Ask yourself whether you actually need to bridge. A lot of the time, there’s a native alternative on the chain you’re already on.
- Avoid protocols that depend heavily on third-party bridges for their core collateral backing. If you’re lending on a platform where the collateral is a bridged or wrapped version of another asset, you’re exposed to that bridge’s security.
- When you do bridge, use established routes with long track records — not new, unaudited solutions chasing higher APYs.
- Never bridge large amounts in a single transaction. Split it up. The few minutes it costs you could save everything if something goes wrong mid-transfer.
2. Check Who’s Behind the Protocol — Not Just the Code
Audits matter. But April proved they’re not enough on their own.
Before you deposit into any DeFi protocol, ask these questions:
- Who are the core team members? Are they doxxed? Do they have verifiable track records? Anonymous teams aren’t automatically bad, but they add risk.
- How is the multisig structured? What’s the threshold? How many people control it? Are those signers public?
- Has there been any recent team turnover? New additions to a team — especially ones with admin access — should be a yellow flag worth researching.
- What’s the incident response history? A project that’s been hit before and communicated clearly, froze contracts quickly, and made users whole is very different from one that went silent.
DeFiLlama, DeBank, and the protocol’s own governance forums are your friends here. Spend 20 minutes before you move $10,000.
3. Simulate Every Transaction Before You Sign
Domain hijacking and wallet drainers have become frighteningly sophisticated. The site looks real. The UI looks right. The URL is almost identical. You click approve, and you’ve just signed away everything in your wallet.
Use transaction simulators. Extensions like Pocket Universe, Fire, and Wallet Guard simulate what a transaction will actually do before it executes. If you’re about to send funds to a contract you don’t recognize, or if a simulation shows unexpected token movements, stop.
Never approve a transaction directly from a link in a Telegram group, Discord DM, or random Twitter reply. Always navigate to the protocol manually through a bookmarked URL.
Check that the contract address you’re interacting with matches the one listed on the project’s official documentation.
4. Don’t Leave Money You’re Not Actively Using in High-Risk Protocols
This one’s uncomfortable to say, but it needs to be said.
That 45% APY on a brand new yield vault? It’s not free money. High yield almost always means high smart contract complexity — more moving parts, more potential failure points, more bridges and oracle dependencies. The higher the APY, the more you should be asking why.
Yield farming is legitimate. But there’s a meaningful difference between:
- Established protocols with years of track record and billions in TVL (Aave, Uniswap, Curve)
- Newer protocols on emerging chains offering exotic yields through complex strategies
Keep your serious capital in the first category. If you want to chase the second category, do it with money you can afford to lose. Treat it like speculation, not savings.
5. Use a Hardware Wallet for Anything Significant
This is the most repeated piece of advice in crypto. It’s repeated because people keep ignoring it.
A hardware wallet keeps your private keys completely offline. Even if you accidentally connect to a malicious site, or your computer is compromised, the attacker cannot move funds without a physical confirmation on the device itself.
The Ledger and Trezor ecosystem are the most established. Set one up. It takes less than an hour. For any wallet holding more than a few hundred dollars in DeFi assets, there’s no excuse not to have one.
6. Revoke Token Approvals Regularly
Every time you interact with a DeFi protocol, you’re usually granting it approval to spend your tokens. Most people approve once and never think about it again.
That means an old protocol you used six months ago and forgot about still has permission to access your wallet.
Tools like Revoke.cash (EVM chains) and Sol Incinerator (Solana) let you see every active approval and revoke the ones you don’t need. Make this part of your monthly routine. It takes ten minutes and can prevent a lot of damage if an older protocol you approved gets compromised later.
7. Don’t Ignore the Red Flags That Are Already There
A lot of April’s victims had warning signs in front of them before the exploits hit.
Things that should make you pause:
- A protocol that had a previous security incident, even a small one
- Sudden changes to contract permissions or multisig configurations without clear explanation
- TVL dropping rapidly with no obvious reason
- Governance proposals that rush through unusual changes to treasury access or contract upgrades
- Bridges or oracle systems that are newly deployed or have limited audit history
You don’t need to be a smart contract developer to spot these. Follow the protocol’s governance forums. Watch the DeFiLlama dashboard for TVL anomalies. Follow reputable on-chain security analysts on X.
Support Our Work
If you found this helpful, consider signing up on OKX or Bybit using our referral links. Your support keeps this content free and flowing.
What the Industry Is Actually Doing About This
It’s not all doom. April’s carnage has triggered real responses.
Aave and a coalition of DeFi firms committed more than $300 million to stabilize the system after the KelpDAO collapse — an intervention that helped normalize yields and restore deposits faster than most expected.
Aave’s upcoming V4 upgrade is specifically designed to reduce reliance on cross-chain bridges, building in native cross-chain functionality that eliminates many of the failure points that made April’s exploits possible.
Standard Chartered called it a sign of DeFi’s growing maturity — the ability to self-organize around a crisis rather than collapse entirely. That framing is optimistic, but it’s not wrong. The sector absorbed a $629 million shock in a single month and kept moving.
AI-driven monitoring systems that flag unusual on-chain behavior in real time are also gaining traction. Several protocols are now exploring insurance-backed protections. Bug bounty programs are scaling up again.
Progress is happening. It’s just happening slower than the attackers are moving.
Also study our guide on how to claim crypto airdrops safely.
The Bottom Line
DeFi is not going anywhere. The opportunity is real. The yields are real. The airdrops and the ecosystem growth and the financial infrastructure being built — all of it is real.
But April 2026 should permanently change how you think about risk management on-chain.
The attacks that drained $629 million last month didn’t hit careless beginners. They hit established protocols, audited code, experienced teams. The shift to social engineering, bridge exploits, and domain attacks means that user behavior — your behavior — has never mattered more.
Check your approvals. Use a hardware wallet. Simulate your transactions. Stay skeptical of new, high-yield, bridge-dependent strategies. And when a protocol gets exploited, read the post-mortem. Every single one of them teaches you something.
The people who build lasting wealth in crypto aren’t the ones who take the most risk. They’re the ones who survive long enough to catch the right opportunities.
Don’t get rekt chasing yield. Stay safe out there.
If you enjoyed this blog, check out our blog on the NFT market’s recovery, related to the DeFi outflow.
As always, don’t forget to claim your bonus on OKX below. See you next time!

Enjoyed this? We cover airdrops, farming strategies, trading setups, and crypto guides every week. Hit follow so you don’t miss the next one.
Source: : airdropalert.com

